 It’s always bad when a service fails. It’s worse when the failure could have been easily avoided. When you’re asked if it would have been possible to prevent the disruption you don’t want to answer; “Yes, but it would have taken ten minutes of my time.” Service failure due to certificate expiration is an example of a scenario which never needs to happen. Check Windows Certificate Expiration is a Nagios Plugin which warns you before a service fails. The plugin is part of Networklore Monitoring pack for Nagios. It is written in Powershell and queries a servers LocalMachine personal certificate store. Some type of certificates you can monitor using other plugins, such as check_http which can monitor certificates on ssl sites. This plugin is intended for other services where you don’t want to open up additional ports, or if you can’t access the certificate directly from your Nagios server. Once you have setup NSClient++ this plugin should take less than ten minutes so install.
It’s always bad when a service fails. It’s worse when the failure could have been easily avoided. When you’re asked if it would have been possible to prevent the disruption you don’t want to answer; “Yes, but it would have taken ten minutes of my time.” Service failure due to certificate expiration is an example of a scenario which never needs to happen. Check Windows Certificate Expiration is a Nagios Plugin which warns you before a service fails. The plugin is part of Networklore Monitoring pack for Nagios. It is written in Powershell and queries a servers LocalMachine personal certificate store. Some type of certificates you can monitor using other plugins, such as check_http which can monitor certificates on ssl sites. This plugin is intended for other services where you don’t want to open up additional ports, or if you can’t access the certificate directly from your Nagios server. Once you have setup NSClient++ this plugin should take less than ten minutes so install.
The default options are as follows
These default values can be changed in three ways.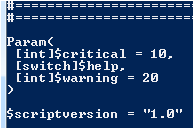
If you send arguments to the script you use the -warning, or -w, to set the warning threshold. The other parameter is -critical or -c. For example if you want the Plugin to warn you 25 days before a certificate expires and return a critical alert 5 days before expiration you would run the script like this:
.nm-check-certificate-expiration.ps1 -w 25 -c 5
Once you download Nelmon the plugin is located in the windows directory.
Please let me know in the comments below, or send feedback if you have questions, feature requests or ideas for other Nagios plugins.