
Have you let the Gophers into your network yet? With Netrasp, you can let them roam wild. Netrasp is a Go package that connects to network devices with SSH to allow you to send commands and configuration to them. The rasping sound as your network gets screenscraped would come from Netrasp. For people coming from the Python world, you could compare Netrasp to Netmiko.

In most of the Python projects I’m working with Pytest is used to test the code, and Coverage is used to check what lines that the tests validate. For this to work, Coverage must take part in the execution of the Python code. While this isn’t a problem for most projects working with NSO poses a challenge since the actual Python code for each NSO package gets executed in a separate Python virtual machine. The goal of this article is to show you how you can overcome this obstacle and gain some insight into your test coverage for your NSO Python packages.
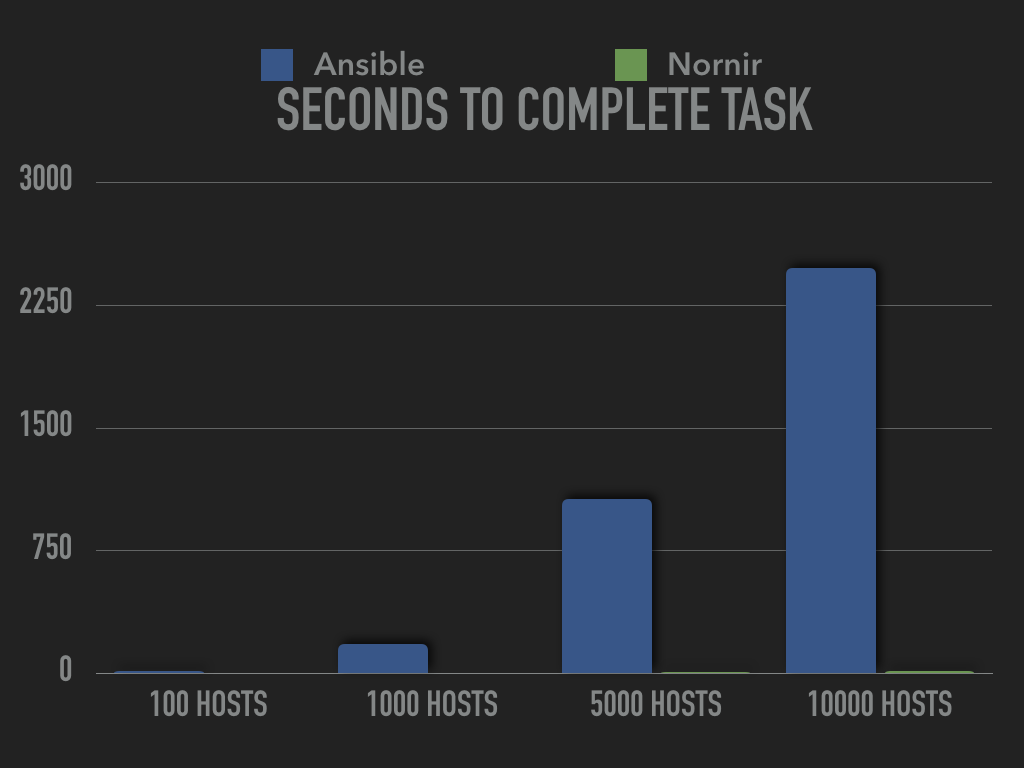
When talking about Nornir and Ansible, speed is one of the topics that come up from time to time. A common argument for Nornir is that it performs better when working with either many hosts or lots of data. For some who hear this, it isn’t entirely clear what we mean. This article will look at some numbers. Recently I came across a quote by Kelsey Hightower that stuck with me. “You haven’t mastered a tool until you understand when it should not be used.” Let’s see if any of that can be applied here.
Nornir is a new automation framework written in Python and intended to be consumed directly from Python. You could describe it as the automation framework for Pythonistas. This might strike you as something wonderful, or it could trigger your spider-sense. Writing code? Isn’t that just for programmers?
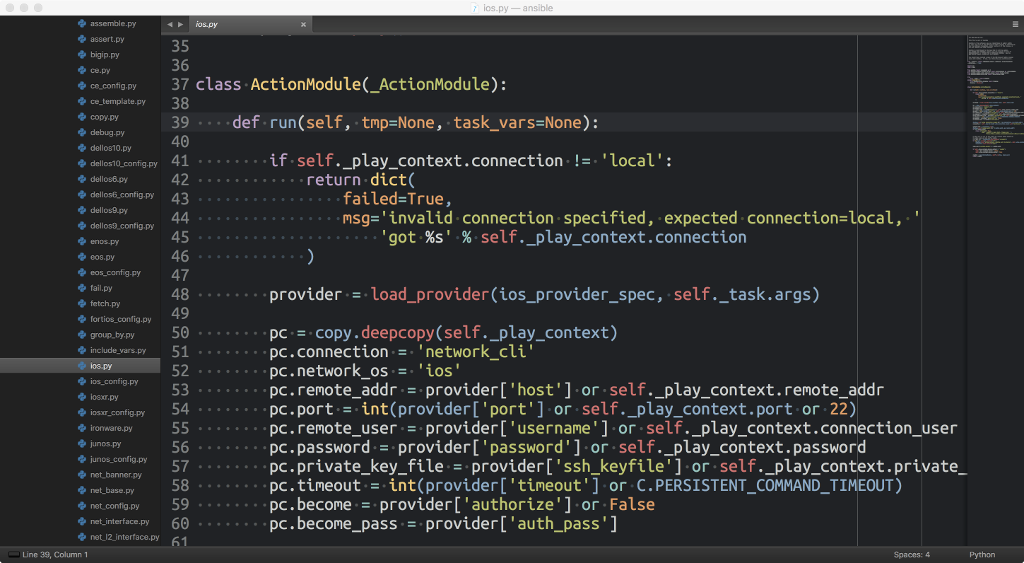
It started out as a question. If you are using several networking modules in a playbook, do you really have to repeat the same credentials on every task? Just like the last few articles about Ansible this one came to life after answering questions in a chat room. The short answer is; No you don’t have to include all of the required parameters for every task, you can use an action plugin to work around that. Great! So what’s an action plugin?

At the outset, a 1200 word article about saving configuration sounds strange. It would perhaps be perfectly normal if the topic was Vi and not Ansible, however there’s a reason for this and its simply speed and itempotency. Saving the configuration in the “wrong” way can take quite a lot of time and one reason for network automation is to accomplish tasks faster and constantly search for ways to improve your processes. This article assumes that you are running Ansible 2.4, but it should work in a similar way regardless.
Aside from being a user, I write about Ansible and try to help others to understand how it works. A few days ago I was answering questions from other Ansible users. Someone was having trouble figuring out why the ios_config module didn’t apply his template correctly. I explained what was wrong with the template, afterwards I thought about the issue some more and realized that the error could potentially be really dangerous. As in a game-over-level-event for your employment dangerous.

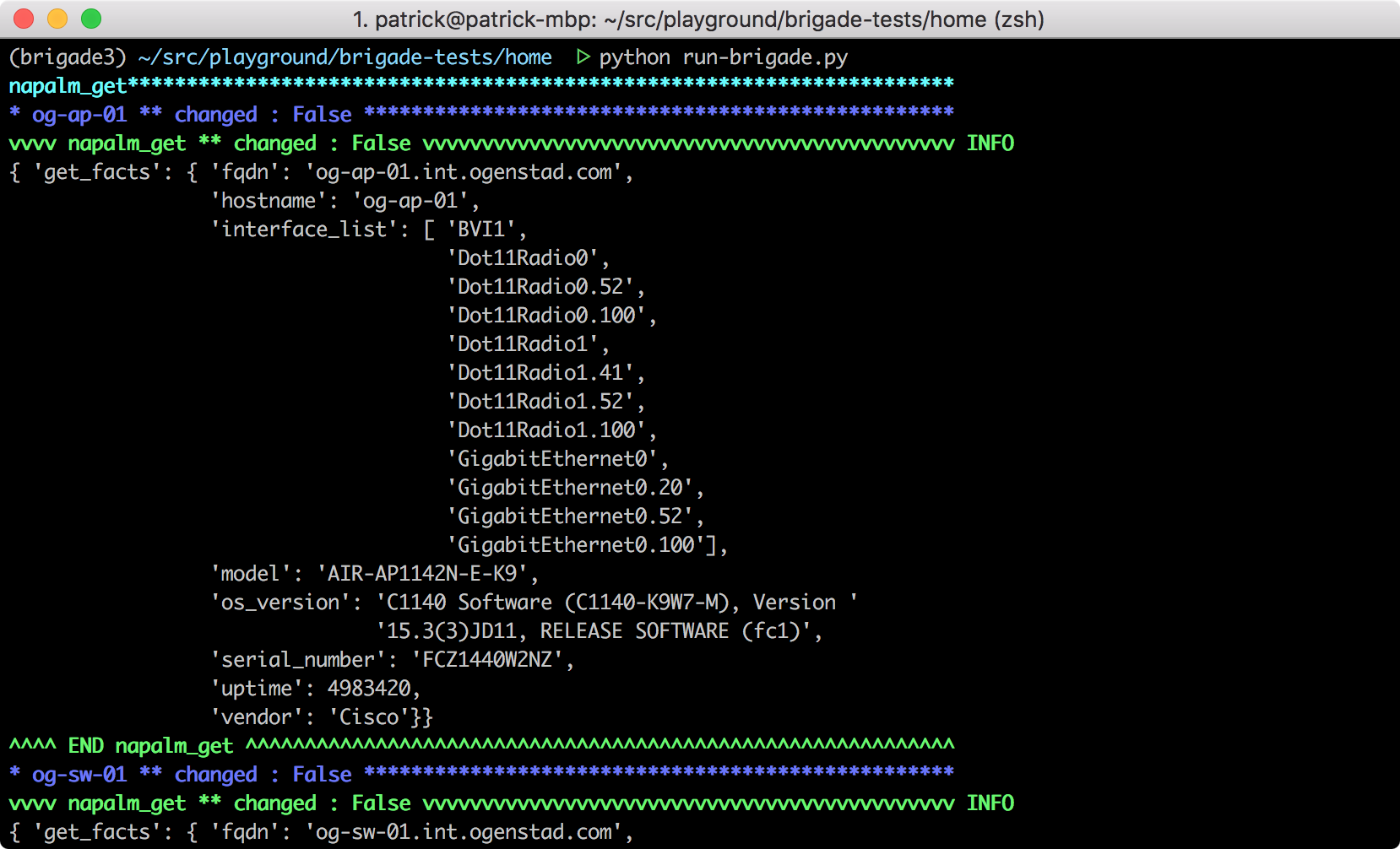
A lot of people who aren’t familiar with Napalm tend to laugh nervously when you suggest they use it in their network. The name Napalm is partly based on getting that perfect acronym and partly a desire to incinerate the old way of doing things and move to network automation. This article is about explaining what Napalm is and what lies behind the acronym.
A lot of new networking modules were released as part of Ansible 2.1. The Cisco IOS, IOS XR, NXOS, Junos and Arista EOS platforms got three common modules, the platform_config, platform_command and platform_template. The command and template modules more or less explains themselves. The config modules have some more tricks to them and I’ve gotten a few questions about how they work. In this article I’m going to focus on the ios_config module and show how you can use it to configure Cisco IOS devices. Future version of Ansible will add more parameters, this article is for Ansible 2.1.
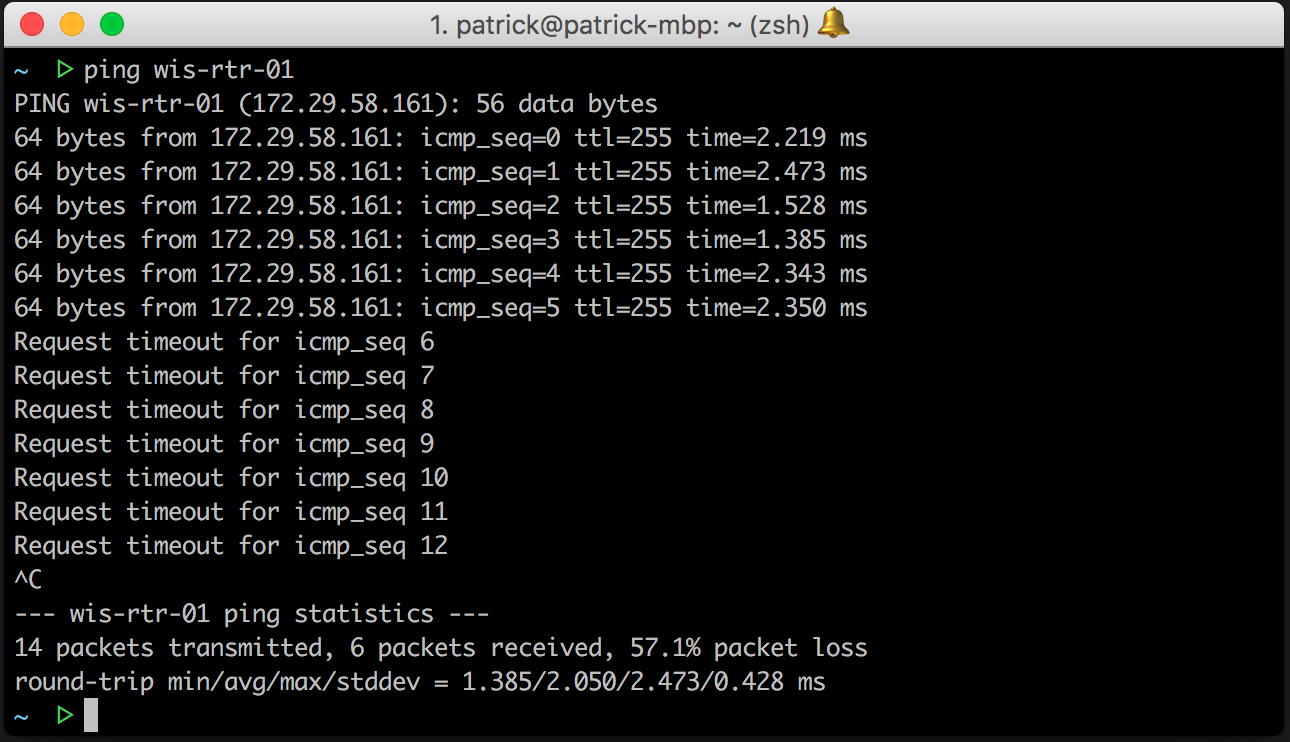
It can get quite exciting when you start to think about network automation and what it can do for you and your network. Once you’ve automated everything you can instead focus on deep work to evolve your business. However this daydream can soon fade away as you start to think about the things you can’t automate, or at least don’t know how to do. Ivan Pepelnjak wrote a piece about automating the exceptions. The post is based on a discussion he had with Rok Papež and his ideas about handling exceptions in an automated way. While the strategy presented is great I think it overlooks some parts when it comes to exceptions that can arise, also the post doesn’t highlight how limitation of the configuration management tools were solved.