Ansible is an open source automation platform. It is very, very simple to setup and yet powerful. Ansible can help you with configuration management, application deployment, task automation. It can also do IT orchestration, where you have to run tasks in sequence and create a chain of events which must happen on several different servers or devices. An example is if you have a group of web servers behind a load balancer. Ansible can upgrade the web servers one at a time and while upgrading it can remove the current web server from the load balancer and disable it in your Nagios monitoring system. So in short you can handle complex tasks with a tool which is easy to use.
Unlike Puppet or Chef it doesn’t use an agent on the remote host. Instead Ansible uses SSH which is assumed to be installed on all the systems you want to manage. Also it’s written in Python which needs to be installed on the remote host. This means that you don’t have to setup a client server environment before using Ansible, you can just run it from any of your machines and from the clients point of view there is no knowledge of any Ansible server (you can run Puppet in standalone mode, but Puppet still needs to be installed). There are some other requirements though, for example if you want to do something related to git on a remote machine a git package must first be installed on the remote machine.
Ansible is available for free and runs on Linux, Mac or BSD. Aside from the free offering, Ansible also has an enterprise product called Ansible Tower.
Once you have installed Ansible and added some hosts to the inventory file, typically /etc/ansible/hosts you can try to connect to your hosts. By default a connection will be made with ssh keys, but you can also specify a username and password.
A good first test is just to see if you can connect to your devices with the ping module.
ansible all -m ping
The “all” keyword is for all of the hosts in your inventory, to only target hosts in a specific group you enter the group name instead of all.
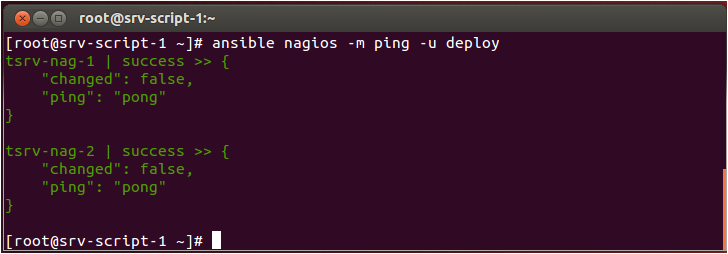
In the above example a connection is made using a user called deploy.
While you are getting started with Ansible it’s easy to run several commands against a group of servers. If you want to update all our Debian machines you could run.
ansible all -i debian-hosts.txt -m raw -a 'DEBIAN_FRONTEND=noninteractive apt-get -qq -y upgrade'
Here the raw module is used to issue a command on all the servers in our debian-hosts.txt file. Another module you will want to try out early is the setup module which gives you information about remote machines.
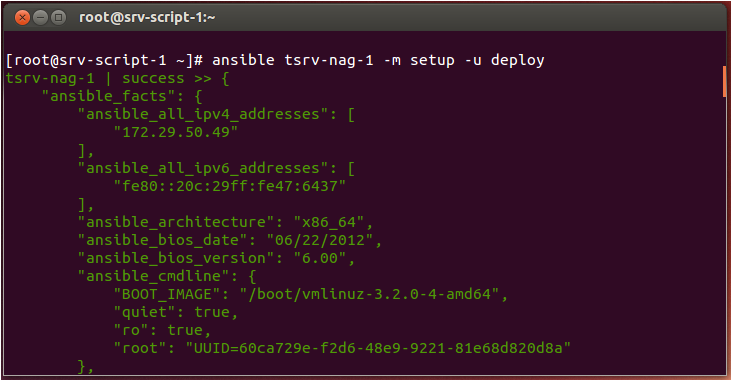
You can use all of the variables found in the setup module to customize what you do with the remote servers.
The real strength of Ansible lies in its Playbooks. A playbook is like a recipe or an instructions manual which tells Ansible what to do when it connects to each machine. Playbooks are written in YAML, which simplistically could be viewed as XML but human readable. When I started using Ansible I’d never looked at YAML, but within hours I was able to write powerful playbooks. Also there are a lot of examples online to help you while you learn.
You could have a Playbook which configures your servers according to a baseline you have defined, so they all are using the correct sshd config and central authentication. Then you use roles for specific server groups. Say you have a groups for web servers, database servers and monitoring servers. Then you decide to add a web server. When you fire off your Playbook, Ansible will install and configure the web server. It will make sure your database server allows connections from the new server, and then add the new server to your network monitoring solution so that you are informed if the server suffers a failure in the future.
Before Ansible has propper support for network devices I wrote some proof of concept code which configured IOS devices using SNMP. Since Ansible 2.1, there’s quite extensive networking support as part of the product. So now it’s no problems to manage network devices with Ansible. The core networking modules within Ansible are all tied to specific platforms. For example theres a ios_config module to configure Cisco IOS devices, for Juniper the module would be junos_config and so on. You can also use the Napalm library from Ansible to automate your network.